Imagine you’re trying to send a secret note in class. Usually, you’d worry about the teacher intercepting it, reading it, and passing it along without you ever knowing. In the digital world, this “interception” happens all the time with our data. Current encryption (like what protects your bank account) relies on math problems that are hard for today’s computers to solve, but will be child’s play for future quantum computers.
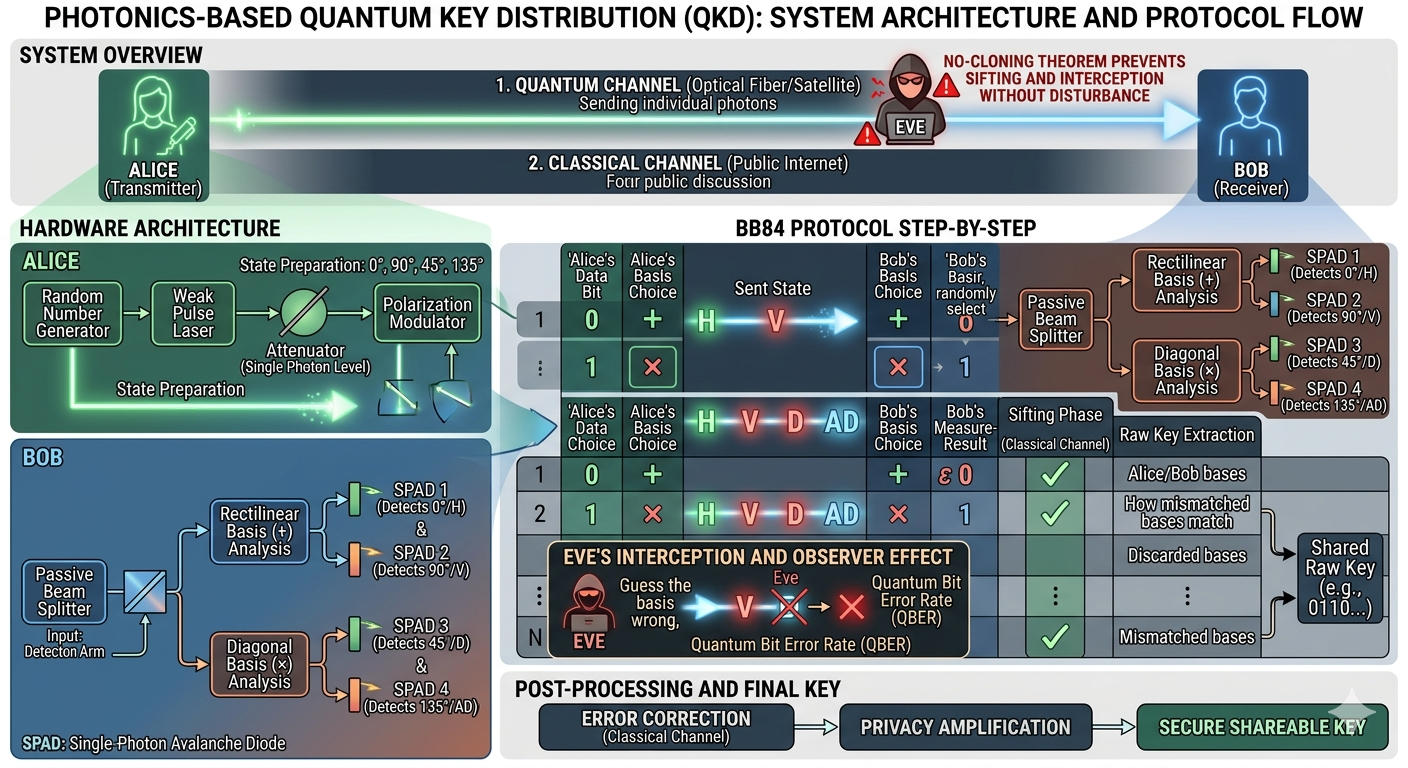
Enter Quantum Key Distribution (QKD). Instead of relying on hard math, QKD relies on the fundamental laws of physics. It uses light particles—photons—to create a shared secret key between two people (traditionally named Alice and Bob). If a spy (Eve) tries to peek, the laws of the universe literally “break” the key, alerting Alice and Bob immediately.
The Technical Landscape: How It Works
At its core, photonics-based QKD uses the properties of light to represent 1s and 0s. The most common method involves polarization—the direction in which a light wave vibrates (e.g., vertical, horizontal, or diagonal).
1. The Quantum Foundation
Two “Golden Rules” of quantum mechanics make QKD possible:
- The Observer Effect: In the quantum world, you cannot look at something without changing it. If Eve tries to measure a photon sent from Alice to Bob, she inevitably alters its state.
- No-Cloning Theorem: It is physically impossible to create a perfect copy of an unknown quantum state. Eve can’t just “copy” the photon and send the original on its way.
2. The BB84 Protocol (The Step-by-Step)
Developed in 1984, this is the “classic” recipe for QKD:
- Preparation: Alice sends a string of individual photons to Bob. For each photon, she randomly chooses a basis (think of this as a filter orientation: either Rectilinear + or Diagonal x and a bit value (0 or 1).
- Transmission: The photons travel through a fiber optic cable or through the air (satellite-to-ground).
- Measurement: Bob receives the photons but doesn’t know which filters Alice used. He guesses and chooses a random basis (+ or x for each photon he catches.
- The Public Sifting: Alice and Bob hop on a regular phone line (the “Classical Channel”) and compare which filters they used. They don’t say what the bit values were—just the filters.
- Key Extraction: If they used the same filter, their bit values must match. They keep those bits and throw the rest away. This becomes their Raw Key.
Detecting the Intruder (Eve)
If Eve tries to intercept the photons, she has to guess the basis to measure them. Because of the Observer Effect, if she guesses wrong, she changes the photon’s polarization. When Bob later measures that photon, there’s a high chance he’ll get an error.
Alice and Bob perform a “Parity Check” on a small sample of their key. If the error rate is too high (usually above 11%), they know someone is listening. They trash the key and start over. If the error rate is low, they use math (Privacy Amplification) to shrink the key and eliminate any tiny bit of info Eve might have stumbled upon.
Why It Matters
- Forward Secrecy: Unlike math-based encryption, which can be recorded today and cracked years later when computers get faster, QKD is secure forever. If you didn’t catch the photon the moment it was sent, that information is gone from the universe.
- Practicality: We already have thousands of miles of fiber optic cables. Companies are now building “Quantum Routers” to make QKD a part of our standard internet infrastructure.
Summary Table: Classical vs. Quantum Keys
| Feature | Classical (RSA/AES) | Photonics-Based QKD |
| Security Source | Mathematical Complexity | Laws of Physics (Quantum Mechanics) |
| Vulnerability | Vulnerable to Quantum Computers | Quantum-Safe |
| Eavesdropping | Can be done silently | Always leaves a physical trace/error |
| Hardware | Standard Chips/Servers | Lasers, SPADs, and Fiber Optics |